WinRoot is designed to unlock features of Session 0 that are not available in interactive user sessions. WinRoot uses the account System (NT AUTHORITY\System) in Session 0 to obtain high privilege that the user normally does not pose. With the help of WinRoot, you can also own what TrustedInstaller owns without modifying ownership.
In Windows Operating Systems, all services and user-mode drivers run in the same session as the first user who logs on. This session is called Session 0. A session consists of all of the processes, windows, window stations and desktops. In Windows XP and earlier versions, all services run along with user applications in Session 0. Since services run at elevated privilege, this situation poses security risks (eg: Shatter attacks). In Windows Operating Systems starting from Windows Vista, this security issue is mitigated by isolating user application to run in a different session rather than Session 0, called as Session 0 isolation. Hence a new session Session 1 is created for the first user who logs in, Session 2 for next user and so on. Since Session 0 is no longer a user session, it is non-interactive. Any attempt that a service makes to render graphics fails. Even though services display a UI, it will be on the default desktop of Session 0 instead of appearing in user’s desktop.
There are various accounts (internal accounts), especially System, Local Service, and Network Service that sign into Session 0. The main benefit of signing into Session 0 with System account is that the process will get all privileges that System account poses. The System account has same file privilege as Administrator account, but they have different functions. Hence we can override restrictions set by domain policy to user and administrator groups using System account.
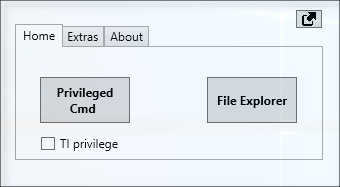
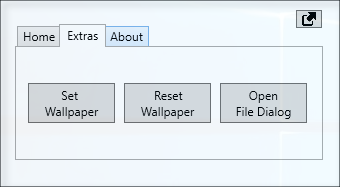
WinRoot can be used to bypass the Session 0 isolation protection and create interactive process even without Interactive Service Detection dialog. The interactive Windows Station WinSta0 is made available and thus the process can display UI and receive user inputs. A separate instance of explorer window can be opened by WinRoot under Session 0, that will help us to browse through files and folders.
The processes are started by WinRoot are under System account (NT AUTHORITY\System), which is a powerful account that has unrestricted access to all local system resources. On using TrustedInstaller, you are getting additional permission – full access and modification permission to WRP (Windows Resource Protection) protected resources are granted in addition to the default privileges of System account. So, you should take care while using the process/apps launched by WinRoot.