.Net Anti-Decompiler is a protective tool for .Net assemblies. It provides an extra layer of security and compliance to your .Net application from reverse engineering. .Net Anti-Decompiler helps in failing class browser tools to reflect your source code. The .Net assembly files .exe and .dll can be protected using this software.
We can’t protect an application from reverse engineering. Any executable file is crackable and we can’t prevent it. Because you don’t make an assembly that the processor can not understand. The only thing that we can do is making the reverse engineering process harder. Obfuscating is not always the best choice. But it does a great job. Breaking the tools that reveals the source code is another approach in application security. The .Net Anti-Decompiler does the same. It is created by understanding how most commonly using de-compiler and class browser tools actually reveals the source code. The following latest version of tools are tested and .Net Anti-Decompiler is found to be successful in preventing the source code revelation.
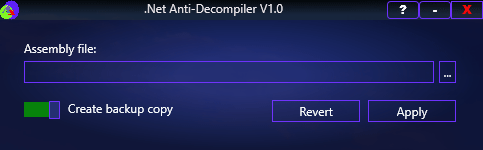
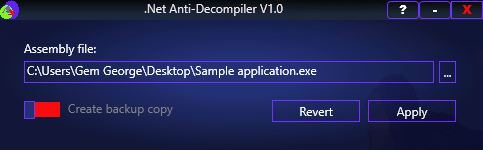
How to work with .Net Anti-Decompiler?
- Obfuscate your application before using .Net Anti-Decompiler (since it is the final layer of protection)
- Browse for the .Net assembly
- Turn off backup button if you don’t want to create backup copy of original application
- Click “Apply” and you are done!
- Incase, if you want to revert the changes done by .Net Anti-Decompiler, click on “Revert” button after browsing the assembly file